SSRF Démasqué : Comment les Hackers Exploitent le Server-Side Request Forgery
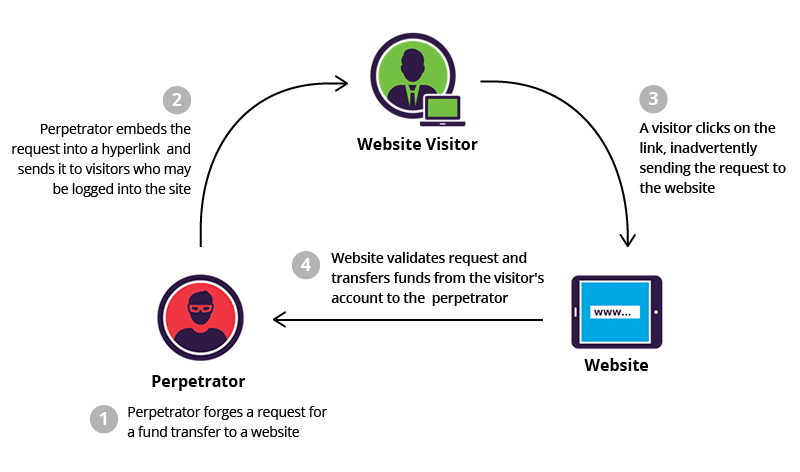
SSRF Démasqué : Comment les Hackers Exploitent le Server-Side Request Forgery Les attaques SSRF, ou Server-Side Request Forgery, sont des vulnérabilités SSRF furtives qui incitent les serveurs à effectuer des requêtes non intentionnelles, exposant souvent des systèmes internes. Cet article