Palo Alto Training – Learn Palo Alto Firewalls in 2025

Computer Security: A Vital Field in the Digital Age Computer Security: A Vital Field in the Digital Age Computer security, also known as cybersecurity, references to the protection of computer systems and networks from various threats like malware, cyber-attacks, data breaks, and unauthorized access. In today's interconnected world, where almost every aspect of our personal [...]
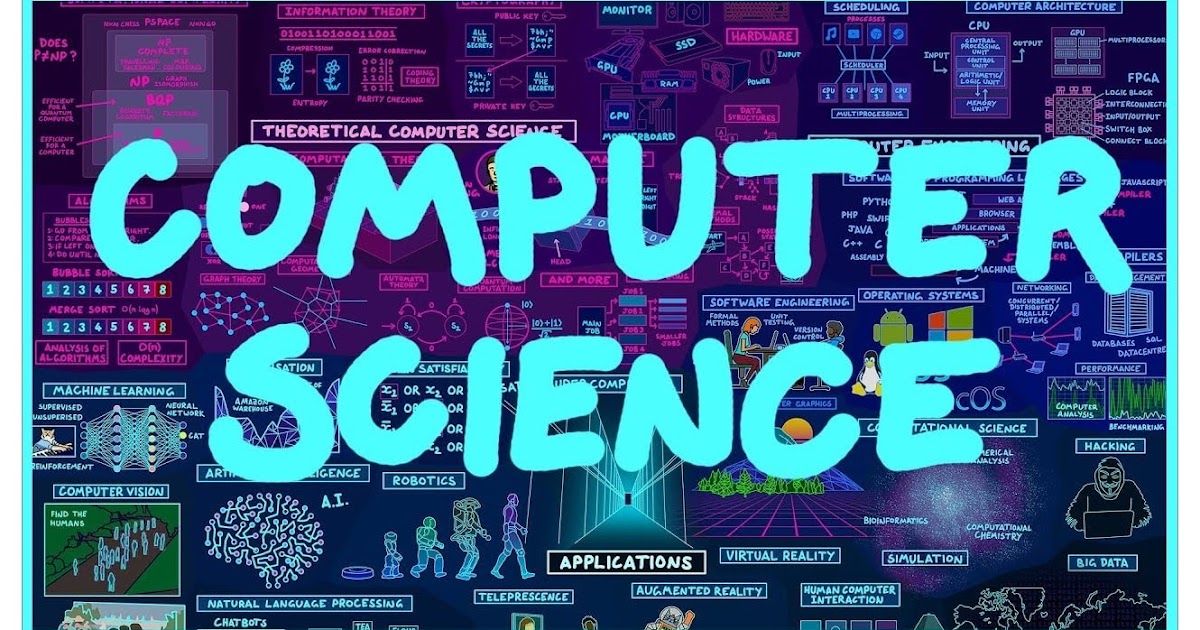
Computer security, also known as Cybersecurity, references to the protection of computer systems and networks from various threats like malware, cyber-attacks, data breaks, and unauthorised access. In today's interconnected world, where almost every aspect of our personal and professional lives connects on digital technology, computer security has become a critical area of focus.
Computer security is an essential aspect of modern life, safeguarding data, applications, and systems from a wide array of threats. By adopting a multi-layered approach to security, including encryption, firewalls, regular updates, and user education, individual and organizations can protect themself from the ever-evolving landscape of cyber threats.
"Protect your digital world—Explore Secure Valley for trusted cybersecurity solutions. "
Get certified with industry-leading cybersecurity certifications from EC-Council, PECB, Palo Alto Networks, and more.

Learn from world-class instructors Collaborate with top professionals Advanced training...

The CEH is the world's leading cybersecurity certification, recognized by...

Onsite training course Led by an instructor Interactive sessions

Asynchronous, self-study environment Video-streaming format Flexible learning schedule
Adding {{itemName}} to cart
Added {{itemName}} to cart

