Palo Alto Training – Learn Palo Alto Firewalls in 2025

Session fixation attacks are a clever session hijacking technique that exploits session IDs to capture user connections. By trapping victims with a predefined session ID via a cookie fixation vulnerability, attackers access without permission once the user is authenticated. This vulnerability of web sessions benefits from a management flaw of [...]
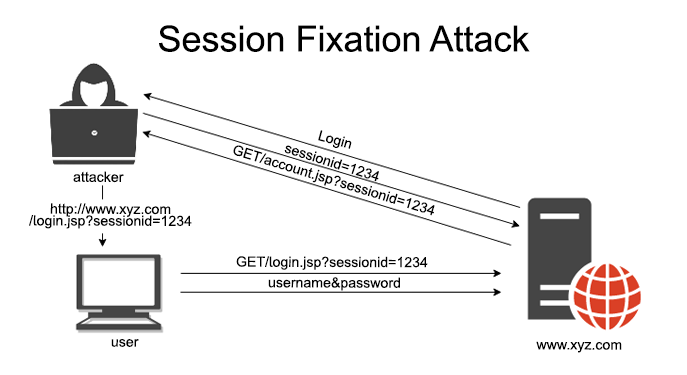
The session fixation attacks are a sessional diversion clever who exploitssession ID operation to capture user connections. By trapping victims with a predefined session ID via a vulnerability to fixing cookies, attackers access without permission once the user has authenticated. This vulnerability of web sessions takes advantage of a session management flaw, often transformed into authentication bypass attack. Recognized in the Guidelines OWASP session schedule, it threatens platforms like the session fixation in PHP, the session fixation in Java used for session fixation in Node.js. In 2025, with the proliferation of web applications, understand the risks of manipulation of session chips and HTTP session attacks is essential. This article explores session fixing examples, real cases and strategies prevention of session fixation to secure your applications.
One session fixation attack prosperity through bad secure session management, allowing attackers to divert active sessions without directly stealing identifiers. Unlike the sessional arrangements vs. sessional diversion, where diversion steals an existing session, the fixation prepares the ground in advance. By operating a vulnerability to fixing cookies, an attacker can force a user to inherit a known session ID, and then wait for the connection to log in. This session management flaw is insidious in the session fixation in ASP.NET or any framework neglecting the Best practices for session regeneration. For companies, this risks taking control of accounts; for developers, this is an alarm signal to strengthen the mitigation of session fixation.
This is how the manipulation of session chips feeds this attack, with practical insights:
One real session fixing case : In 2010, a banking application did not regenerate session IDs, allowing attackers to divert accounts via phishing links. Tools such as Burp Suite facilitate session fixation detection. Pricing Section : In 2025, certifications to master this include: € – 2,500 €), OSCP (2 100 € – 2,500 €), WAHS (500) € - 1,500 €), CISSP (800 € - 1,200 €), CompTIA Security+ (350 € - 400 €). WAHS covers the session fixation in ASP.NET, while OSCP deepens the session fixing defence models.
The prevention of session fixation based on a secure session management Robust. Here's how to protect your systems:
For more information, see Wikipedia or Gartner. LUniversity of Rennes 1 offers suitable training.
The session fixation attacks divert connections via sessional diversion, exploiting the Web session vulnerabilities of the session fixation in PHP to the session fixation in Java. With the manipulation of session chips and authentication bypass attacksThis threat listed by OWASP session schedule requires action. The real violations underline the need for session fixing defence models. Certifications as WAHS and OSCP equip you with skills in secure session management. Explore them certification cybersecurity training in SecureValley Training Center to protect your users today!
Get certified with industry-leading cybersecurity certifications from EC-Council, PECB, Palo Alto Networks, and more.

Learn from world-class instructors Collaborate with top professionals Advanced training...

The CEH is the world's leading cybersecurity certification, recognized by...

Onsite training course Led by an instructor Interactive sessions

Asynchronous, self-study environment Video-streaming format Flexible learning schedule
Adding {{itemName}} to cart
Added {{itemName}} to cart

