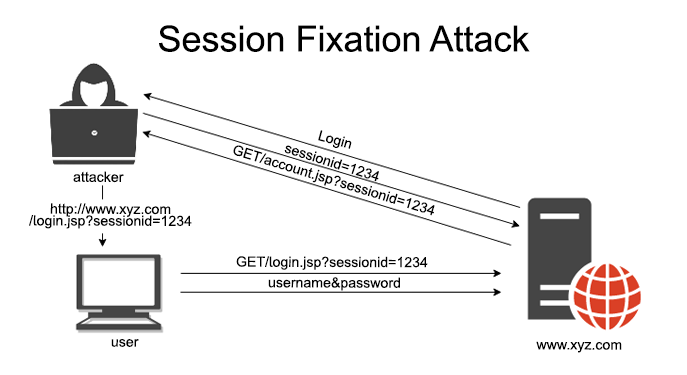
Session Fixing: The Attack That Hijacks User Logins
Session fixation attacks are a shooting session hijacking technique that exploit session ID exploitation to take over user logins. By tricking victims into using a pre-set session ID via a cookie fixation vulnerability, attachments gain unauthorized access once the user authenticates. This web session vulnerability raisings a session management